Summary
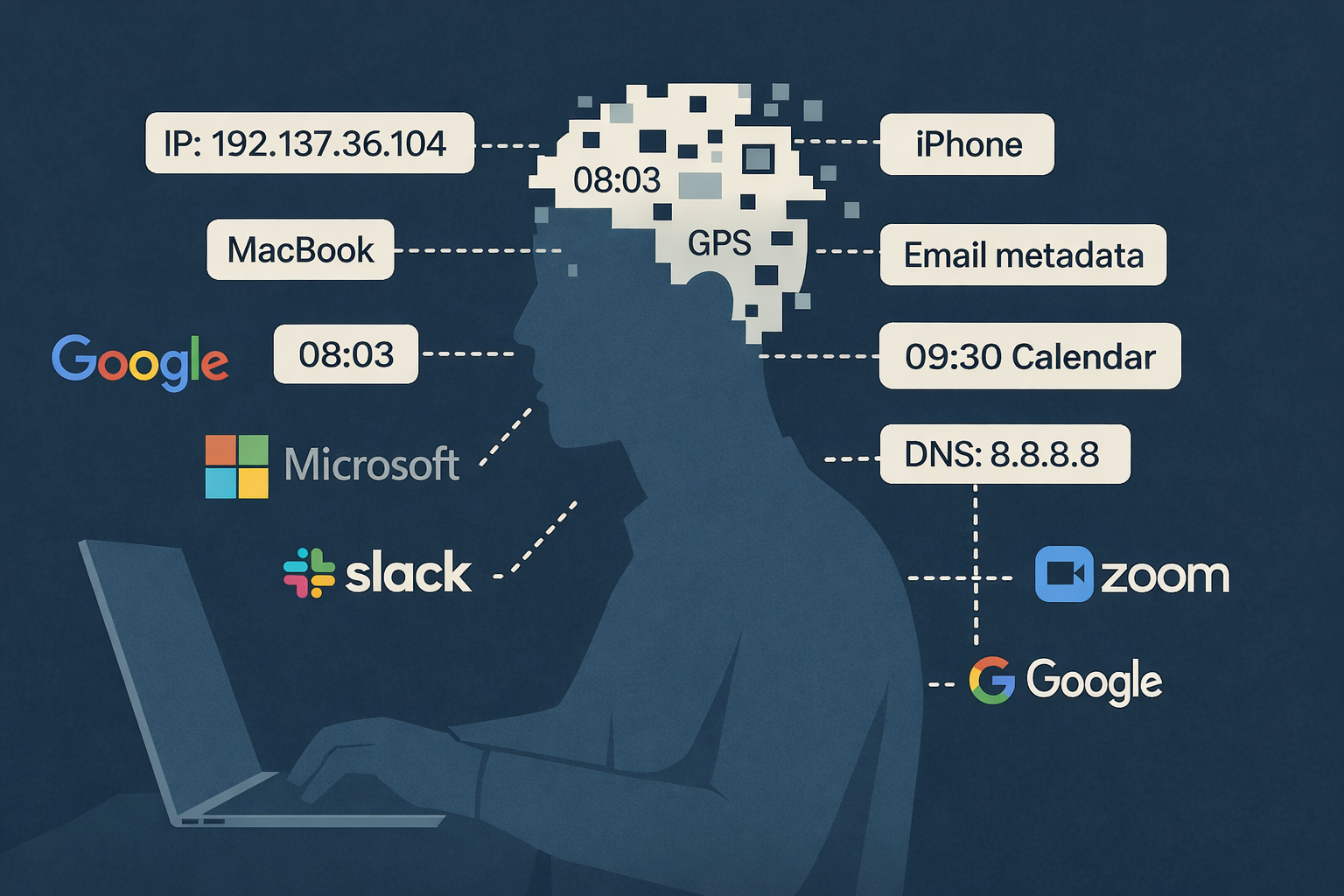
This article explains how metadata — who communicates with whom, when, and from where — can reveal identity, behavior and relationships without ever accessing content. It argues that metadata has shifted from a passive trace to an active intelligence layer, and that controlling the metadata layer is now a structural concern for infrastructure design.
You don’t need to be hacked to be monitored.
Logging in, opening a document, replying to an email — the very behaviors we are trained to perform daily — are enough.
This is the reality of metadata.
Metadata is often described as “data about data”, but in practice it functions as a behavioral layer. It describes interactions, timing, relationships and patterns rather than content.
Over time, these signals form a highly accurate representation of how systems — and people — operate.
The shift from passive data to active intelligence
What has changed in recent years is not the existence of metadata, but how it is used.
Metadata is no longer stored passively. It is processed continuously, enriched with external data sources and analyzed automatically.
Patterns are detected, relationships inferred and anomalies surfaced in near real-time.
This transforms metadata from a supporting layer into a primary intelligence layer.
Why this matters more than many assume
The common assumption is that privacy risk begins when someone reads your messages, opens your files or gains access to the substance of your communication.
But at scale, metadata often delivers enough context on its own.
Who you speak to. When you do it. How often. From where. On which device. In what sequence. With what rhythm.
That is often enough to infer relationships, habits, working patterns and changes in behavior.
And once those patterns are available across multiple systems, a profile starts to emerge whether anyone intended to build one or not.
The architectural question
This creates a fundamental question for infrastructure design:
Who controls the metadata layer?
Because control of metadata determines who has visibility into behavior.
And visibility, at scale, becomes influence.
Designing modern systems is therefore not only about securing content, but about controlling what is observable.
Encryption still matters. But transport security does not prevent correlation, logging or jurisdictional access to surrounding data.
A system can be technically secure while still being behaviorally transparent.
Practical implications
Organizations should consider:
- minimizing unnecessary telemetry
- reducing external dependencies
- understanding data flows across systems
- choosing infrastructure aligned with jurisdictional control
- treating metadata as a governance issue, not just a privacy note
This is not about paranoia.
It is about architecture.
This connects to the wider dependency layer explored in when the grid goes dark, and to the architectural questions raised in surveillance and security.
Why does metadata matter for privacy?
Metadata matters because it reveals patterns of behavior without accessing content.
Even when communication is encrypted, metadata can still show:
- relationships between individuals
- frequency of interaction
- location and timing patterns
This makes metadata a primary source of insight in modern systems.