Summary
Finland is now investigating the Valtori breach as suspected espionage after police said the stolen dataset may affect Finland’s security and cause harm.
A breach at Finland’s state IT provider, Valtori, is now being investigated not only as an aggravated data breach, but also as suspected espionage. That alone makes the case notable. What makes it far more interesting is why the classification changed. Finnish investigators are not saying that the stolen data suddenly turned out to be classified documents, nor have they publicly identified a foreign state actor. Instead, the National Bureau of Investigation says the stolen dataset itself may, when combined, reveal information that affects Finland’s security and can cause harm. That is a very different threshold from an ordinary breach story.
“It is possible that by combining the information in the data content, one may be able to form information that affects Finland’s security and can cause it harm.” (translated)
— Aku Limnell, Detective Chief Inspector, Finnish National Bureau of Investigation, via KRP
That sentence changes the entire reading of the case. Because once police say that, this is no longer just about leaked administrative records. It becomes a question of whether a technical management dataset can help reconstruct parts of the Finnish state: who belongs where, how devices and users are organized, how ministries and agencies may be grouped, and where high-value roles or dependencies may sit. The real danger may not be what was stolen record by record, but what can be built from it afterwards.
What was actually exposed
According to Valtori’s initial statement, the breach was identified on 30 January 2026 in the mobile device management service it provides to the Finnish state. Valtori said the incident concerned configuration and user data related to around 20,000 government mobile devices, and that the attacker exploited a zero-day vulnerability in the software used in the service. A follow-up update added that the attacker had accessed information used to operate the service, including names, work email addresses, phone numbers and device details. Valtori also said that, based on current information, no data stored directly on the mobile devices themselves had been compromised.
That distinction matters. This does not appear to be a case where content was simply pulled from phones or tablets. The more serious layer was the control plane around them: the administrative and technical data used to manage a state-wide mobile environment. In other words, the breach appears to have hit the management layer rather than the user-content layer. That is precisely the kind of data that can look dry in a headline, but become strategically sensitive when viewed as a whole.
Why the Finland angle makes this serious
The scale also widened significantly as the investigation progressed. On 6 February, Finland’s Prime Minister’s Office said the breach affected staff across all ministries. It also said that Valtori’s system had not actually erased deleted records, but had only marked them as deleted. As a result, user and mobile device data from all organizations that had used the service during its lifecycle may have been compromised. That takes the story well beyond a limited incident affecting one technical environment at one point in time. It suggests that a historical, state-wide administrative dataset may have been exposed.
That is what makes this a Finland story, not merely an IT story. If a dataset spans all ministries’ staff and includes historical user and device records from organizations that used the service over time, then the issue is no longer just the exposure of names and phone numbers. The issue is whether the data can be used to build a structural picture of the Finnish state’s mobile administration environment: ministries, agencies, administrators, device groupings, high-value officials, technical patterns and organizational boundaries. That is exactly the kind of aggregated visibility a foreign intelligence service would find useful even without direct access to content on the devices themselves.
“The nature of the data has not changed from what was originally reported. The data mainly contains configuration and user information.” (translated)
— Aku Limnell, via KRP
“The classification of the crime has been refined through clarifying the nature of the dataset as a whole, not because of a possible suspect actor or perpetrator.” (translated)
— Aku Limnell, via KRP
That second statement is crucial. It means the seriousness of the case appears to have increased because investigators developed a clearer picture of what was stolen and what could be inferred from it, not because they had publicly solved attribution. In other words, the data itself raised the stakes.
This is not “just metadata”
The phrase “just metadata” obscures more than it explains in cases like this. Configuration data reveals how systems are built and administered. User and device data reveal how they are organized and used. At the scale of a state mobile management platform, those elements can begin to describe the environment itself: who belongs to which organization, which devices are managed together, how control may be segmented, and which people or functions may be more valuable to target next. The risk here is not necessarily a single dramatic record. It is the intelligence value that emerges when many ordinary-looking records are combined.
That is also why the case is analytically stronger than a normal “large breach” headline. It is not only about volume. It is about whether administrative data from a government MDM platform can be transformed into operational understanding. If so, then this is not just a privacy incident or a data-protection failure. It becomes a national-security problem.
What this could actually enable
The most realistic risk is probably not that someone suddenly gained direct access to everything on government phones. Valtori has said it has no indication that data stored directly on the devices themselves was compromised. The more important question is what the management-layer data could enable next.
At minimum, a dataset like this can support target selection. Names, work email addresses, phone numbers, device identifiers and configuration data from a government-wide MDM environment can help an adversary identify high-value individuals, understand which users sit close to key institutions, and select people for follow-on phishing, vishing or impersonation attempts. It can also support organizational mapping: not just who works in government, but how ministries, agencies, technical domains and administrative layers may be grouped in practice. And beyond that, it can support operational preparation by giving an adversary a better basis for planning future access attempts, social engineering, supplier targeting or broader intelligence collection.
That is likely why the case has moved beyond ordinary breach language. The concern is not only exposure, but enablement: what the dataset may allow an adversary to do next. The real danger may not be what was directly stolen, but what can be built from it afterwards.
The wider European backdrop
There is also a broader European context. Valtori said the breach involved exploitation of a zero-day vulnerability in a commercial mobile management product and that no corrective patch was available when the vulnerability became public on 29 January. According to Valtori, the update was installed immediately once available and the service was isolated from the network.
The broader Ivanti EPMM wave has been tied to active exploitation of CVE-2026-1281 and CVE-2026-1340, two critical vulnerabilities publicly described as enabling unauthenticated remote code execution on vulnerable systems. See advisories from Ivanti, CERT-EU, and CSSF.
Finnish reporting also places the case in the same broader Ivanti wave that affected public-sector environments elsewhere in Europe, including Denmark, the Netherlands and the European Commission. That does not, by itself, prove common attribution in the Finnish case. But it does support a more serious reading of the incident: the MDM layer itself appears to have been an attractive target in a broader campaign affecting government environments.
The harder question for government IT
A central government ICT provider would normally be expected to have vendor advisories, CERT channels, vulnerability intelligence feeds and rapid patch-assessment routines in place. But this case also shows the limit of that model when exploitation begins before a fix exists. If Valtori’s account is correct, the compromise landed in the gap before a patch was available. That makes the harder questions even more important: segmentation, hardening, monitoring, exposure control and data minimization.
The historical data issue is particularly difficult to ignore. If deleted records were not truly erased, then the consequences of one compromise could be magnified by years of retained administrative data. In security terms, retained data is still exposed data. And when that retained data describes a state-wide device management environment, the resulting risk is no longer merely technical or administrative. It becomes structural.
Closing
The most important thing about the Valtori case is not simply that Finland suffered a large breach. It is that investigators appear to have concluded that the compromised MDM dataset may be capable of describing enough of the Finnish government’s structure to create national-security risk. That is a different category from a standard personal-data incident. It suggests that the real issue is not simply exposure of names, phone numbers or technical fields one by one, but the possibility that combined user, device and configuration data can be used to build a structural picture of the state.
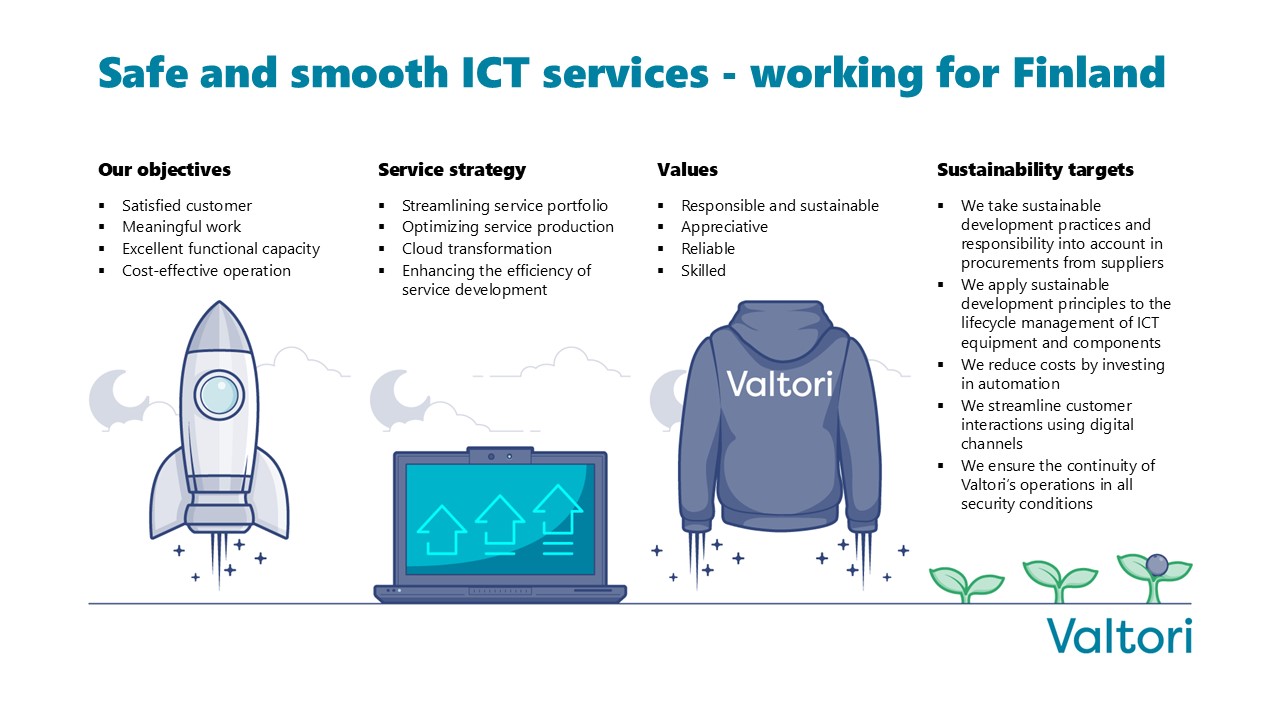
There is also a trust dimension here. Valtori describes itself as developing, maintaining and protecting the country’s largest ICT environment, and its public messaging emphasizes secure and seamless government ICT. Yet on its own website, the public communication around this case appears relatively narrow and largely concentrated in early February. That may well reflect the constraints of an ongoing investigation. But from the outside, it also reinforces the impression that one of the state’s most central ICT actors has said comparatively little, publicly, about a case that later grew into suspected espionage.
And that is why this case deserves attention. Not because espionage has already been proven. Not because officials have publicly named a foreign intelligence service. But because Finland’s own police are saying, in effect, that the dataset may be dangerous precisely because of what it becomes when assembled: not just records, but a map.
Sources
- Finnish National Bureau of Investigation, 21 April 2026
- Valtori: Data breach in part of central government mobile device management, 3 February 2026
- Valtori: Update on the mobile device management data breach, 5 February 2026
- Prime Minister’s Office of Finland, 6 February 2026
- Valtori front page
- Ivanti: Security Advisory for Endpoint Manager Mobile (EPMM) – CVE-2026-1281 and CVE-2026-1340
- CERT-EU: Threat Intelligence Briefing on active exploitation of Ivanti EPMM vulnerabilities
- CSSF: Active exploitation of vulnerabilities on Ivanti Endpoint Manager Mobile (EPMM)